After 3 months of good preparation I passed a challenging GIAC Certification for the GXPN – GIAC Exploit Researcher and Advanced Penetration Tester.
The highlights for me were to learn and really understand how to defeat Windows and Linux stack protection, find common mistakes in cryptography implementation and in general to create and customize the tools to make them work for you.
A guide to how I got the GXPN Certification.

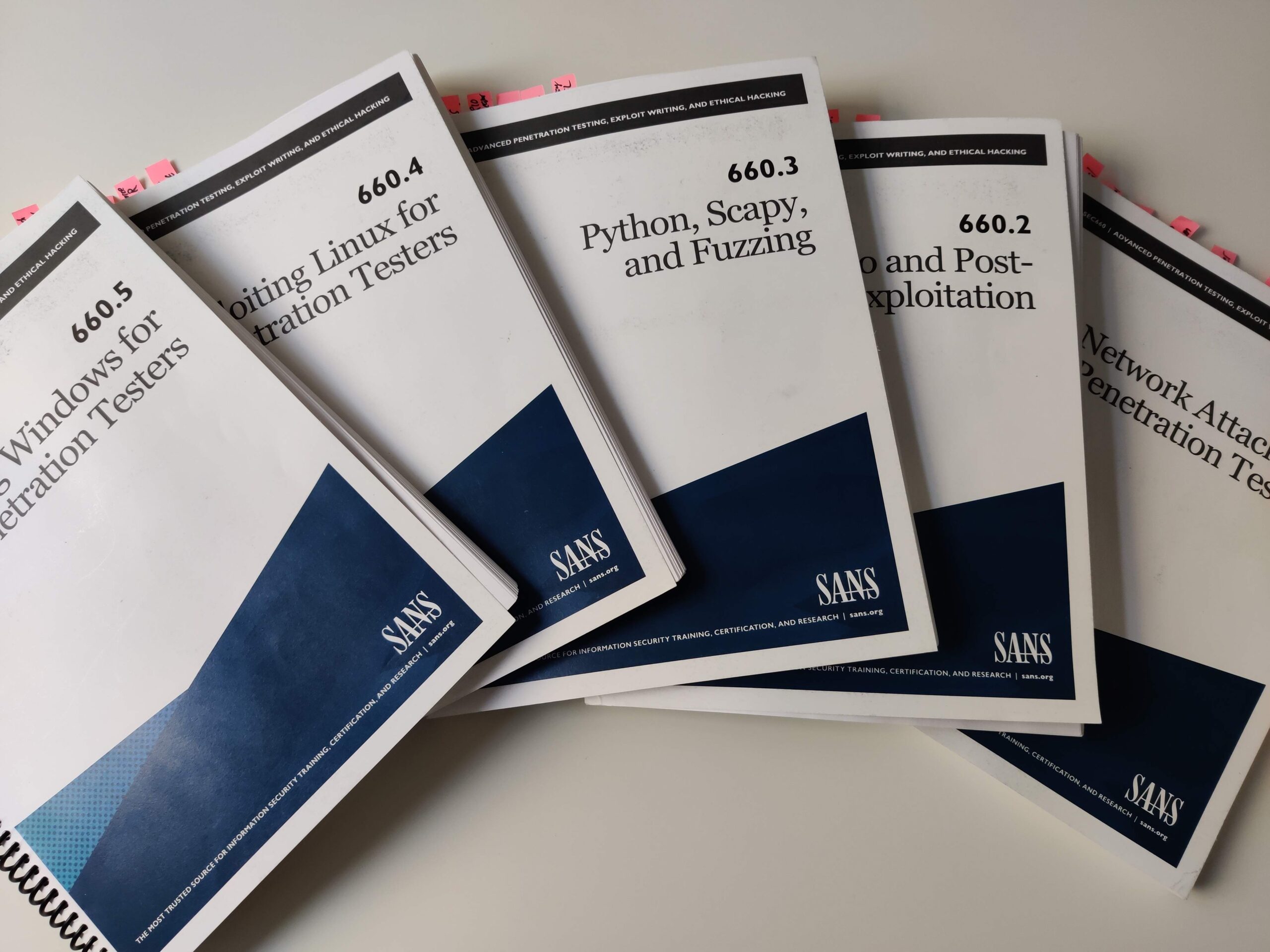
The SANS SEC660 “Advanced Penetration Testing, Exploit Writing, and Ethical Hacking” course
For me it was the first SANS training and also the first On Demand course. You get two virtual machines. I had to repeat some of the exercises several times. Sometimes the videos are slightly different from the screenshots in the books which is good because multiple ways to solve the tasks are shown. The authors also explain the reasons why they do it the way they do and share a few background information to these tools.
On an older review, I read how it was commented that many old tools were used that were no longer maintained. In the 2020 SEC660 course version I had, the new versions of the tools were also presented, but also immediately the errors of the newer versions. Again, it stands out who this course is aimed at. Namely to pentesters who can rewrite existing tools or develop their own tools to adapt them to their use cases – which is required in some exercises. Some of the course authors are maintainers of these tools themselves or have provided their fork.
The GXPN exam
The GXPN certification is one of the most advanced pentest certifications and is aimed at experienced security professionals. Certifications like OSCP or GPEN are a good prerequisite to take the next step towards GXPN. The GXPN is similar to the OSCE syllabus in the network part.
I can only recommend to take the two practice exams. Especially to deal with the nature of the tasks. Here I could again internalize where I had deficits. Finding the correct Stack Pointers and gadgets! The last 6 questions are virtual machines that are provided in the browser. There is also a virtual keyboard, which I needed for example for the pipe “|” because I’ve been using a German keyboard. Since I had the impression that the last practical challenges are weighted very strongly it was important to me to have still sufficient time available for the practical challenges.
My background:
I chose the SEC660/GXPN course because it has only very little overlap with my previous certifications. My pentesting experience so far has been at the web application level. I already knew the Windows stacks from my studies and I did some debugging with Cheat Engine before. Finding buffer overflows, tricking out the stack protections, that was all new to me. My experience with Python helped me a lot in developing my own scripts with Scapy. That’s where I saved some time in the course.
- Web application-level pentesting experience
- Bachelor’s in CS
- Comfortable in programming with Python
- Basic Windows stack knowledge
How I did prepare for the exam:
- Take the On Demand course
- Did all the Lab exercises
- Use the provided VMs
- While watching the exercises I created for each challenge a cheatsheet with the used commands
- Take both practice tests – highly recommend doing them
- Went though the book again and highlighted some phrases
- Created a index/cheatsheet based on my notes from the exercises – you are allowed to take this with you to the exam

Exam Objectives
- Accessing the Network: The candidate will demonstrate an understanding of how to bypass network access control systems.
- Advanced Fuzzing Techniques: The candidate will be able to develop custom fuzzing test sequences using the Sulley framework.
- Advanced Stack Smashing: The candidate will demonstrate an understanding of how to write advanced stack overflow exploits against canary-protected programs and ASLR.
- Client Exploitation and Escape: The candidate will demonstrate an understanding of bypassing or exploiting restricted Windows or Linux client environments, and exploiting or interacting with client environments using tools like Powershell.
- Crypto for Pen Testers: The candidate will be able to attack and exploit common weaknesses in cryptographic implementations.
- Exploiting the Network: The candidate will demonstrate an understanding of how to exploit common vulnerabilities in modern networks attacking client systems and common network protocols.
- Fuzzing Introduction and Operation: The candidate will demonstrate an understanding of the benefits and practical application of protocol fuzzing to identify flaws in target software systems.
- Introduction to Memory and Dynamic Linux Memory: The candidate will demonstrate a basic understanding of X86 processor architecture, Linux memory management, assembly and the linking and loading process.
- Introduction to Windows Exploitation: The candidate will demonstrate an understanding of Windows constructs required for exploitation and the most common OS and Compile-Time Controls.
- Manipulating the Network: The candidate will demonstrate an understanding of how to manipulate common network systems to gain escalated privileges and the opportunity to exploit systems.
- Python and Scapy For Pen Testers: The candidate will demonstrate an understanding of the ability to read and modify Python scripts and packet crafting using Scapy to enhance functionality as required during a penetration test.
- Shellcode: The candidate will demonstrate the ability to write shellcode on the Linux operating system, and demonstrate an understanding of the Windows shellcode methodology.
- Smashing the Stack: The candidate will demonstrate an understanding of how to write basic exploits against stack overflow vulnerabilities.
- Windows Overflows: The candidate will demonstrate an understanding of how to exploit Windows vulnerabilities on the stack, and bypass memory protections.
Overall
GIAC publishes a list with the names of all certificate holders. Currently there are only about 2.600 GXPN analysts. So the GIAC GXPN certification is a real niche. I learned a lot while preparing for the GXPN, but it was also very challenging and took more time than I initially thought. I would do it again though, I haven’t had such a steep learning curve in a long time.
“The penetration testers who have to sit back and wait for someone else to develop attack tools will always be one step behind the defenders.”
SANS SEC660 Books
Well explained. I want to take private training with you in order before I take the On Demand course. Is it possible and are you ready to do that?
The on demand course is very well explained that you won’t need private training. You can re-watch the courses as often as you like.