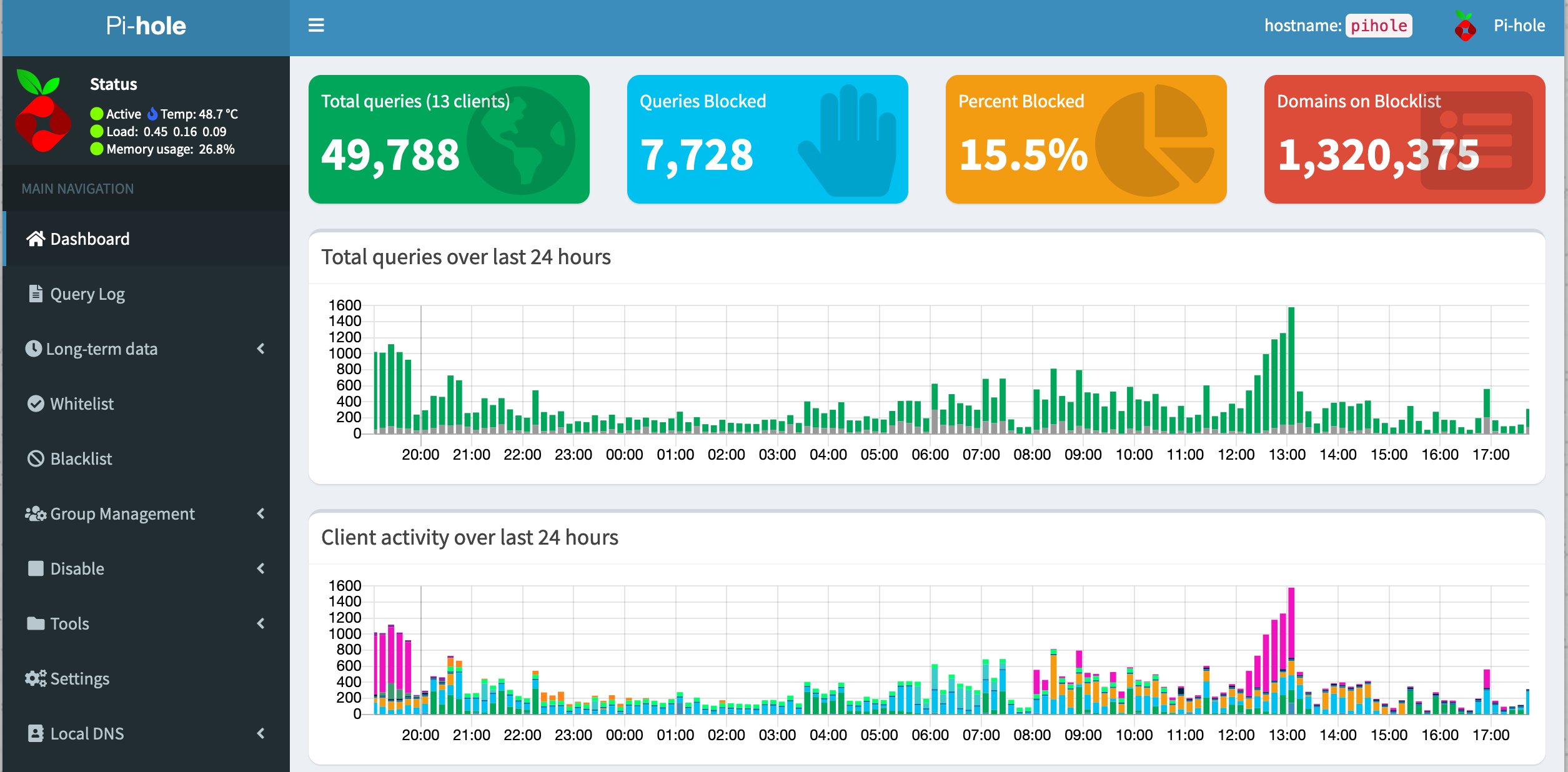
I installed the Pi-hole on a Raspberry Pi. Pi-hole is a DNS server for your home network. I have it running on a Raspberry Pi 1, so it’s nice to have a use for my old Raspberry here. It also runs on a Raspberry Zero. Pi-hole is a DNS sinkhole (/blackhole) and is used to block unwanted domains without installing any software on the clients.
I use my Pi-hole mostly…
- to block phishing, cryptomining, spam and malware sites
- to block ads and advertising pages
- to block telemetry data
and this …
- on all devices (Smart TV, IoT, PC, mobile)
- without installing any tools on your devices
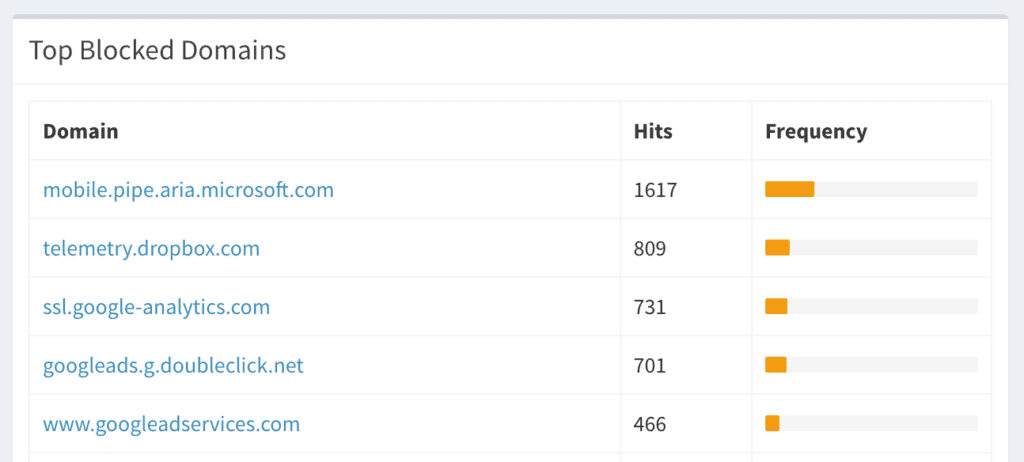
Instead of blocking ads via browser add-ons, a DNS server can do this globally for all devices and browsers. This means that even the Smart TV no longer shows ads. Also the cheap IP-Cams from China cannot send telemetry data home. All requests which are using a domain to connect are logged and can also be manually added to the block list.
You can use public filter lists as source but you can also add custom domains you want to have blocked. Now I would like to share with you my personal collection of filter lists that I have put together. I have been running very well with them for several months now.
First I would like to gather together what is especially important to me about these lists:
- A suitable source are the lists as used by the browser add-ons of the antivirus manufacturers. The lists are actually publicly available. They can even be sniffed if you want to use the same list from a specific add-on you’ve used before.
- The filter list should be updated regular. There are many outdated list available on GitHub. Select only filter lists which are updated daily. No phishing attack will take place on an old domain which is known for sharing malware.
- Use the same lists as tools like Google Safe Browsing. I’ve reported some phishing pages before and it does take just a few hours until a new phishing page is part of such a huge filter list as the Google Safe Browsing list. Many other commercial and cooperate DNS filters use this as a source too.
I’ve moved my filter list collection to a GitHub repository because there it will be better maintained.
Hi,
I just installed pihole on my new Pi 4, version Pi-hole v5.8.1 FTL v5.13 Web Interface v5.10.1. I am used to pihole using many blocklists, but this new pihole has offered just one blacklist during installation (the StevenBlack list, of course), and I am absolutely unable to add any additional blacklist (I almost crashed google by searching for useful hints).
Using the admin’s Web GUI, almost all addressses (even the original StevenBlack list address) are being refused, claiming invalid characters.
Furthermore, even if I succeded in adding a “minimal” address (i.e. without any slash), it is not being used when updating gravity.
So, how can I add any blacklist which will be accepted by gravity aupdates?
Please help me…
-Jens
I am using Pi-hole v5.8.1 FTL v5.13 Web Interface v5.10.1 and it is working fine. I can add blacklists via the admins GUI. Have you tried to run “pihole repair”. If your system fails that hard I would try to reinstall it.