For WordPress there are very comprehensive scanning tools like WPScan. Unfortunately it is not quite the same with the CMS TYPO3.
Typo3 describes in its Security Guideline detailed measures to secure the Typo3 instance. Beside the use of secure passwords, always current versions etc. there is also a great area about permissions and access restriction. Let’s hope people are following these written guidelines 😉
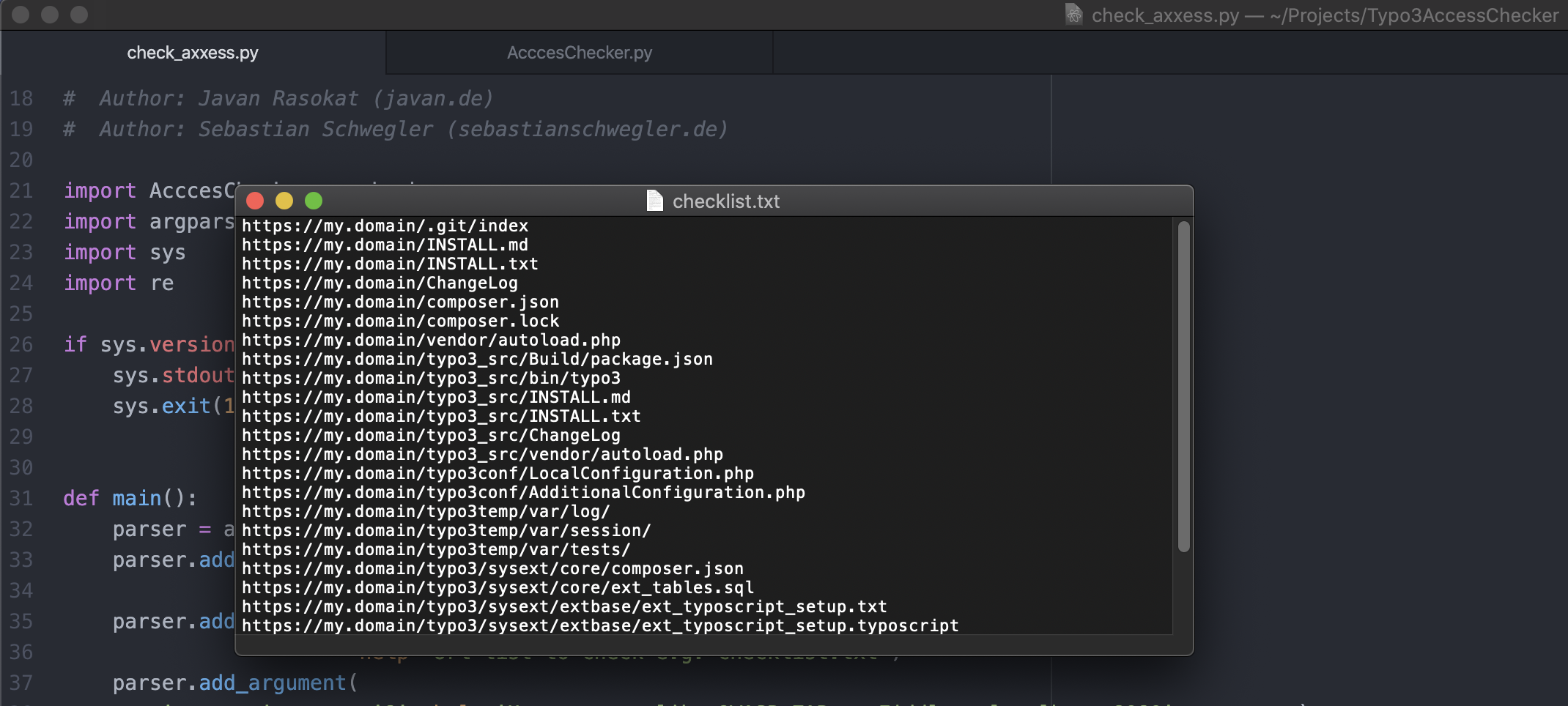
Together with Sebastian we’ve created a simple scanner, which scans these endpoints of a Typo3 instance. There is no other tool that does this job for us.
This scanner focuses on the access restrictions. With not too much astonishment we had to find out while testing our tool that many of the Typo3 instances on the Internet have obviously skipped the step from the installation manual to secure them.
It is very important to recognize these missing access restrictions. Because without them every visitor can call the ChangeLogs of Typo3 and the installed extensions. This increases the danger of a successful attack through e.g. vulnerable extensions, exposing backup and config files and more.
If you are just about to pentest a Typo3 CMS or want to check your own instance, I can recommend the following tools and pages:
- https://github.com/JavanXD/Typo3AccessChecker – Check if Typo3 security guidelines are followed.
- https://github.com/whoot/Typo3Scan – Typo3 Enumerator: Enumerates extensions to gain information about outdated and vulnerable extensions.
- https://typo3.org/help/security-advisories – TYPO3 Security Advisories
- https://docs.typo3.org/m/typo3/reference-coreapi/master/en-us/Security/GuidelinesAdministrators/Index.html#restrict-access-to-files-on-a-server-level – TYPO3 Security Guidelines